Analysis of the Android Anatsa Banking Trojan
A new banking trojan called "Anatsa" is targeting several banks around the world. This is a short analysis of the malware.
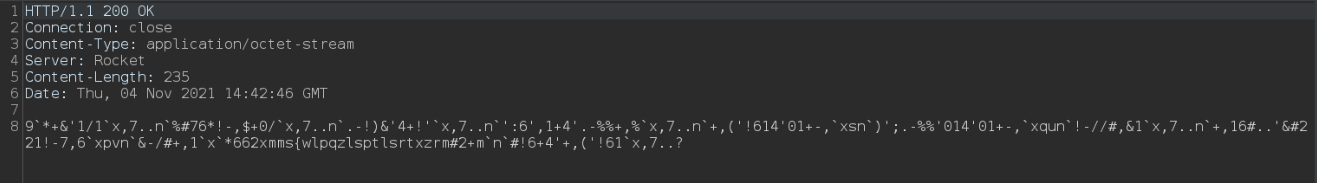
The host replies with the following message
Depending on the returned "is_last_version" parameter, the vicitm has to update the app
And allow the installation from unknown source
The alleged update downloads the second stage of the trojan
UI of the second stage
Permission request
Once permissions has been granted, the C2C Server is contacted
Here is the current configuration of targeted banks:
| uk.co.hsbc.hsbcukmobilebanking com.chase.sig.android com.wf.wellsfargomobile com.citi.citimobile com.konylabs.capitalone com.infonow.bofa com.jpm.sig.android com.usbank.mobilebanking com.truist.mobile com.pnc.ecommerce.mobile com.tdbank com.schwab.mobile com.statestreetbank.grip us.hsbc.hsbcus com.citizensbank.androidapp com.syf.synchronybank com.creditonebank.mobile com.monitise.client.android.clydesdale com.fidelity.android us.current.android com.robinhood.android com.moneylion com.sablemoney.sableapp.prod com.virginmoney.uk.mobile.android com.monitise.client.android.yorkshire com.monitise.client.android.clydesdale com.algorand.android com.coinbase.android co.mona.android com.monese.monese.live com.binance.dev com.danskebank.mobilebank3.uk com.rbs.mobile.android.ubn com.rbs.mobile.android.natwest com.rbs.mobile.android.natwestoffshore com.plunien.poloniex com.triodos.bankinguk com.wallet.crypto.trustapp com.cooperativebank.bank uk.co.metrobankonline.mobile.android.production com.starlingbank.android io.metamask co.uk.getmondo com.binance.us com.kraken.invest.app com.blockfolio.blockfolio com.gemini.android.app com.okinc.okcoin.intl com.barclays.android.barclaysmobilebanking com.tideplatform.banking com.grppl.android.shell.halifax com.grppl.android.shell.CMBlloydsTSB73 com.usaa.mobile.android.usaa com.blockfi.mobile com.marcus.android com.unionbank.ecommerce.mobile.android org.penfed.mobile.banking com.navyfederal.android com.stash.stashinvest com.regions.mobbanking com.varomoney.bank com.current.app com.huntington.m com.clairmail.fth com.mint piuk.blockchain.android com.q2e.texasdowcreditunion5004401st.mobile.production pr.com.firstbank com.oneazcu.banking com.axos.udb com.etrade.mobilepro.activity org.suncoast.mobile com.firsttech.firsttech org.ncsecu.mobile org.ncsecu.mobile com.softek.ofxclmobile.warrenfcu com.bethpage.bethpage com.myoccu.mobile com.ifs.banking.fiid3160 com.desertschools.mobilebanking com.nymfcu.nymfcu com.softek.ofxclmobile.summitcu com.fi7453.godough com.cuamerica.cuamerica com.ifs.banking.fiid3337 com.ksfcu.ksfcu com.ifs.mobilebanking.fiid9094 com.scottcreditunion5029.mobile com.socalcu.socalcu com.q2e.unitedfcu5017android.ufcu.uwnmobile com.credituniononecu.credituniononecu mobile.dcfcu.org com.ifs.mobilebanking.fiid3919 com.ifs.banking.fiid1359 com.growfinancialfcu.growfinancialfcu com.nexowallet com.investvoyager com.mobileloft.alpha.droid mbanking.NBG com.vivawallet.business gr.winbank.mobilenext com.EurobankEFG io.sperax.wallet ru.sberbankmobile ru.otpbank.mobile ru.letobank.Prometheus ge.lb.mobilebank com.idamob.tinkoff.android ru.bankuralsib.mb.android gr.nbg.go4more com.ubanksu ru.vtb24.mobilebanking.android com.mtbank com.columbiabank3685.mobile.production com.capital.etf.trade ch.raiffeisen.twint ch.postfinance.twint.android com.csg.creditsuisse.twint ch.postfinance.android com.csg.cs.dnmb com.ubs.swidK2Y.android com.ubs.swidKXJ.android com.neonbanking.app ch.raiffeisen.android com.flowbank.client ch.bankcler.zak com.axa.android.smartclaims.ch ch.zkb.slv.mobile.client.android com.swissborg.android ch.zkb.twint ch.zkb.frankly ch.bcv.mobile.android |
Anatsa has remote access capabilities which makes it very dangerous. It avoids the user from clicking the app details on the phone. The screen disappears immediately. Uninstalling of the app is therefore not possible.